Editor’s Note: This blog entry was originally published on February 1, 2017, and was updated on December 18, 2019.
Who Needs to Be Concerned about Payment Security? Everyone.
While you may have heard the news stories in recent years of data breaches at large retailers like Target and Macy’s, large retailers aren’t the only targets of credit card data breaches. Small businesses, while less lucrative for cybercriminals, can present easy pickings if the merchants accept credit cards and haven’t taken basic steps to secure their payments environment. Here’s what ISVs and their merchants of any size can do to reduce the risk of having thieves access their customers’ sensitive credit card data.
Payment Security Tips
Global Payments Integrated recommends a multi-pronged approach to payment security, combining EMV, encryption and tokenization to keep cardholder data safe. Here are a few ways for ISVs and their merchants to keep payments secure.
Limit Stored Data
With credit card payments accepted in-store and online, there are a number of opportunities for merchants to store personal payments data, physically and digitally. Credit card data is often maintained for customer convenience – for repeat and return purchases, for instance. However, stored data (sometimes referred to as “data at rest”) is vulnerable to hackers and malware. Businesses should aim to eliminate or limit storage of cardholder data. When storage is necessary, this data must be stored securely and according to the individual PCI compliance requirements.
Encrypt & Tokenize
The safest course of action to protect customer information is to move it out of the merchant environment altogether. Where does one move it? Payment vaults in the cloud are offered by a number of processors, permitting access to stored data when needed for a transaction. At first blush, this would not seem more secure, as data is in transit and, therefore, accessible. This method is rendered safe through the proper use of encryption and tokenization. The data is still accessible in transit, but is encoded and converted into digital tokens which cannot be deciphered without the decryption key.
Embrace EMV
EMV is a fraud-reducing technology that protects against losses from the use of counterfeit cards. The majority of credit cards now include the EMV smart chip, generating a new code for every transaction, making the card virtually impossible to falsify and re-use. The chip interacts with hardware devices and payment networks to ensure the card is authentic. In industries where card fraud is a concern, merchants should obtain the hardware and software necessary to accept the new payment standard.
Leverage Security Experts
Payments security is complex and changing constantly as new technologies emerge. Businesses should select a payment processor or partner who can help analyze systems, identify vulnerabilities and deploy solutions to prevent unauthorized access to customer information. Small businesses must now have their payment applications and terminals installed by Qualified Integrators and Resellers (QIRs). These security professionals are trained and certified to install and maintain PA-DSS validated payment applications.
Global Payments Integrated Payments Security Solutions
Unsure where to start when it comes to payments security? Global Payments Integrated can help. Global Payments Integrated maintains that the answer to keeping sensitive payment data safe is a multi-pronged approach incorporating EMV, QIR, encryption, tokenization and more.
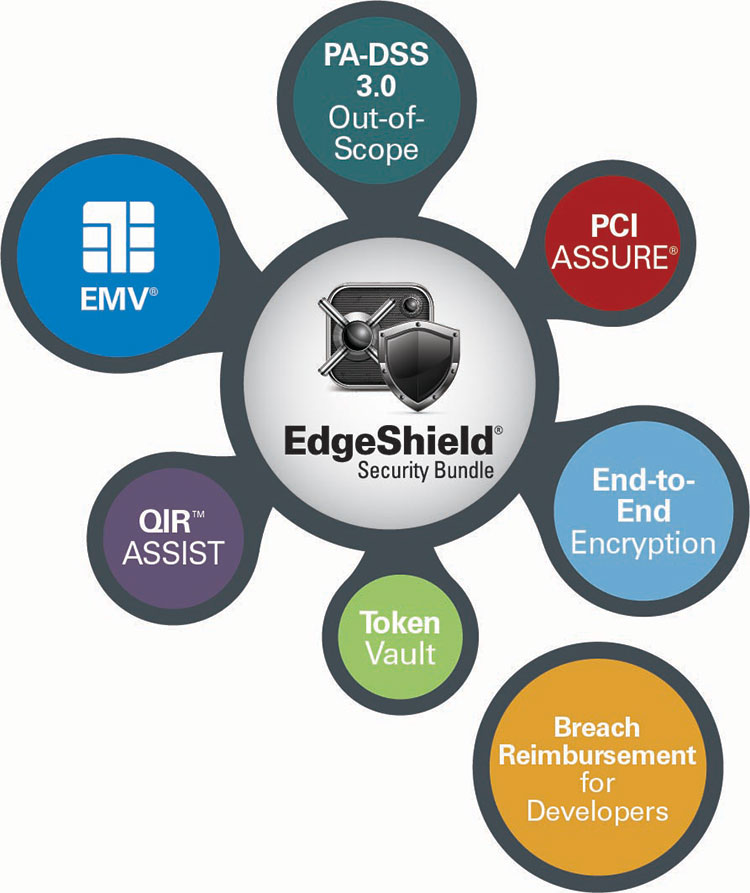
EdgeShield Security Bundle
Our EdgeShield Security Bundle is an advanced security services bundle intended to protect credit card data, prevent counterfeit fraud, and enhance payments security. Through a unique collection of complementary security solutions, EdgeShield delivers one of the industry’s most secure payments platforms.
- The Global Payments Integrated EMV Solution - This fraud-reduction technology protects card issuers, merchants and consumers from losses due to the use of counterfeit and stolen payment cards at the point-of-sale. It helps insulate developers from complex device driving and card brand certifications.
- E2E Encryption - Global Payments Integrated’s proprietary end-to-end encryption is designed to render cardholder data unreadable, encrypted at the device. Merchants are unable to view card numbers after the swipe, dip or hand-key.
- Token Vault - Cardholder data is replaced by digital "tokens" based on this technology. Sensitive data is stored in the secure Global Payments Integrated vault rather than in the merchant environment.
- PA-DSS 3.0 Out-of-Scope - Payment applications are rendered out-of-scope with EdgeShield, eliminating cumbersome PCI validation requirements.
- PCI ASSURE - EdgeShield includes the PCI ASSURE program to help merchants simplify PCI compliance with online access to self-assessment questionnaires, network scans, a breach reimbursement program, and custom security profiles generated from the business’ processing activity.
- Global Payments Integrated QIR Solutions
- Global Payments Integrated: QIR Certified - The security experts at Global Payments Integrated have achieved QIR certification and can ensure your small business merchants are using payment applications installed and serviced in accordance with PCI standards.
- Get Certified: QIR ASSIST - For developers who wish to pursue QIR certification, Global Payments Integrated offers QIR ASSIST, a support program to get your staff certified and ensure you have access to payments security best practices.
Conclusion
A credit card data breach can be disastrous for a small business - but with the right security measures, it’s preventable. Contact Global Payments Integrated today to learn more about our security solutions.
